At the Huawei Network Summit 2026 (HNS 2026) held last week in Cairo, Huawei and its industry partners released the ‘Xinghe AI Full-Scope Security Campus Technical White Paper’ detailing “all-domain awareness and proactive intelligent defense” in the age of AI. The paper contains technical details of Huawei’s approach to Post-Quantum Cryptography (PQC) and Quantum Key Distribution (QKD) for networks, with a focus on PQC.
Huawei’s recommended PQC algorithms
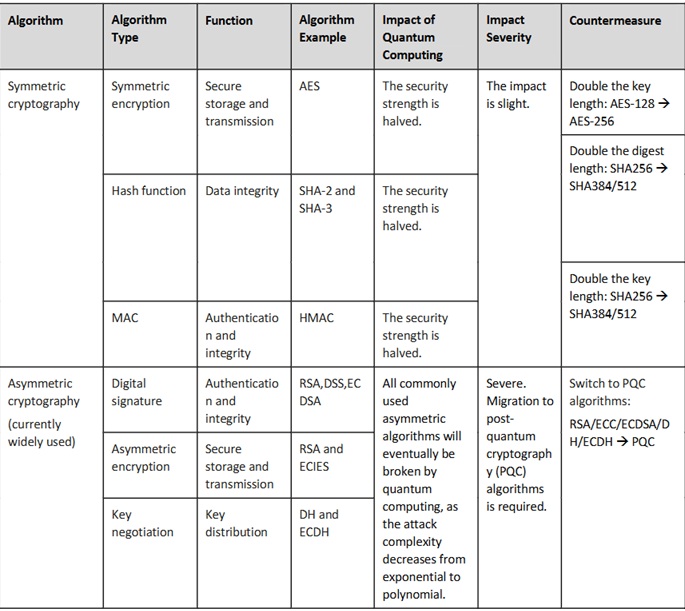
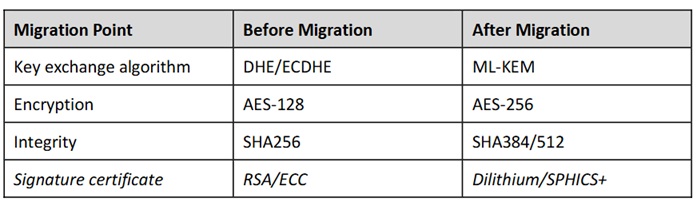
The paper states, “The following table illustrates the impact of quantum computing on secure communication
algorithms currently used in campus networks. For symmetric encryption algorithms, it is necessary to strengthen key lengths—for example, AES-256 encryption is generally considered resistant to quantum computer attacks. For asymmetric key algorithms, solutions that can resist quantum cracking need to be considered.”
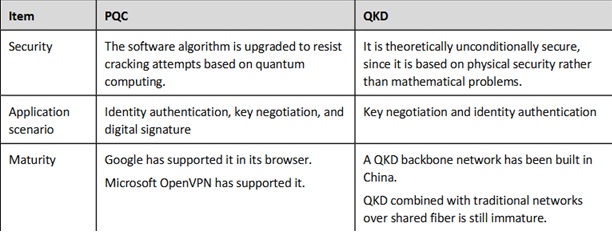
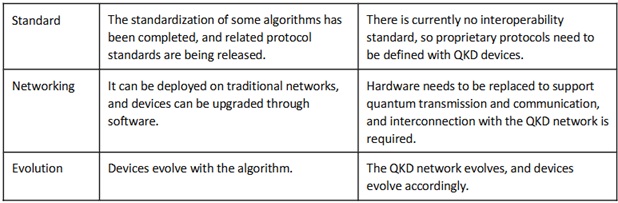
PQC vs QKD
The paper also compares compares PQC and QKD, arguing that QKD is more suitable for communication over Wide Area Networks (WANs), while PQC is better suited for intranets.
PQC for Network Planes
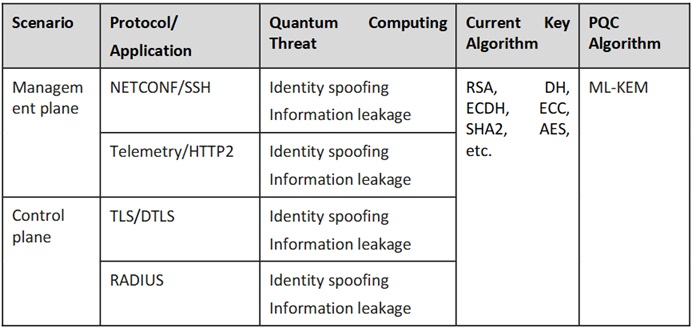
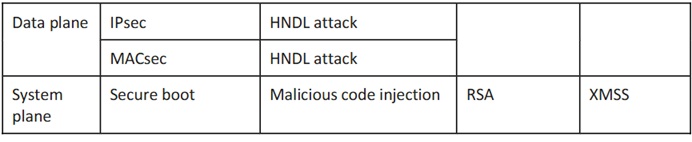
The paper recommends that for campus network architecture, PQC transformation should be considered across multiple dimensions, including the management plane, control plane, data plane, and system plane.
The following table summarizes the main considerations:
Migration for SSH Protocol
The paper uses the examples of the Secure shell (SSH) and Transport Layer Security (TLS) protocols to illustrate the PQC migration process.
The paper states that for SSH, for example, key negotiation process relies on the traditional Diffie–Hellman (DH) exchange protocol, and therefore risks being broken by quantum computing. It recommends the following:
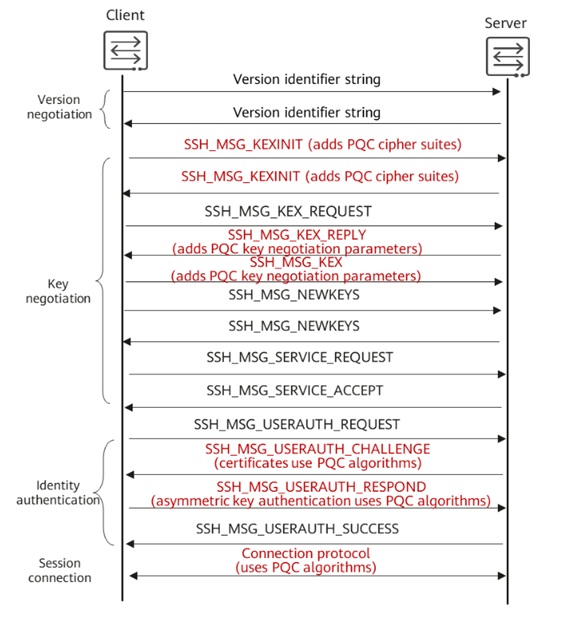
Alternative algorithms for SSH
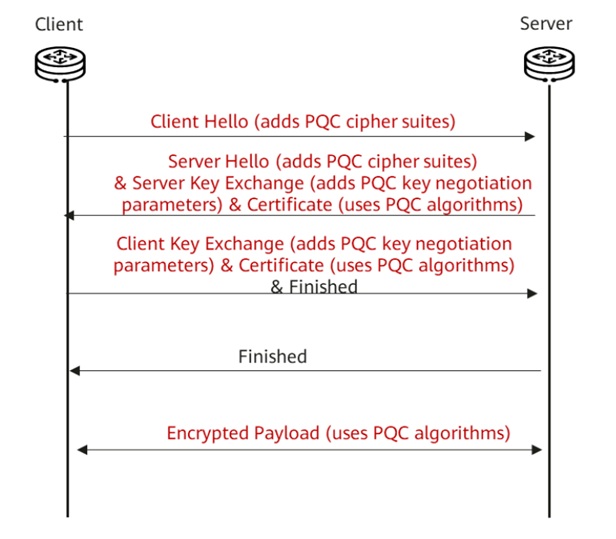
Migration for TLS Protocol
The paper states that TLS 1.3 is required for TLS to support PQC algorithm transformation, because TLS of earlier
versions does not support this. The TLS 1.3 protocol adds PQC cipher suites to the key negotiation process, while retaining the original DH/ECDH algorithm negotiation. Once TLS supports PQC, applications implemented on top of TLS—such as HTTPS, BGP over TLS, NETCONF, and RADIUS—will also be able to support PQC. The paper also states that TLS transformation should follow the same logic as that of SSH.
Read the full white paper here.